Regardless of Apple’s finest efforts, Mac malware does exist, we describe some circumstances under. Nonetheless, earlier than you panic, Mac malware and viruses are very hardly ever discovered “within the wild”.
Now and again you’ll hear of huge profile trojans, malware, and ransomware that’s focusing on the Home windows world, very hardly ever is that this a menace to Macs. For instance, the worldwide WannaCry/WannaCrypt ransomware assault that hit again in Might 2017 was solely focusing on Home windows machines and due to this fact no menace to Macs.
Fortunately Apple has varied measures in place to protect towards such threats. For instance, macOS shouldn’t permit the set up of third-party software program except it’s from the App Retailer or recognized builders. You possibly can verify these settings in macOS Ventura’s System Settings > Privateness & Safety and scroll to the Safety part, or, if you’re utilizing Monterey or older, go to System Preferences > Safety & Privateness > Common. You possibly can specify whether or not solely apps from the Mac App Retailer will be put in, or if you’re comfortable to permit apps from recognized builders too. If you happen to had been to put in one thing from an unknown developer Apple would warn you to verify it’s authenticity.
As well as Apple has its personal built-in anti-malware device. Apple has all of the malware definitions in its XProtect file which sits in your Mac, and each time you obtain a brand new software it checks that none of these definitions are current. That is a part of Apple’s Gatekeeper software program that blocks apps created by malware builders and verifies that apps haven’t been tampered with. For extra info learn: how Apple protects you from malware. We additionally talk about whether or not Macs want antivirus software program individually.
In recent times malware on the Mac really decreased, nonetheless, as you will notice for those who learn on, Macs are usually not utterly protected from assaults. Even Apple’s Craig Federighi has admitted there’s a downside, saying in Might 2021 that: “We now have a stage of malware on the Mac that we don’t discover acceptable.” To remain protected, we suggest you learn our finest Mac safety suggestions and our spherical up of the finest Mac antivirus apps, by which we spotlight Intego as our prime decide.
One other factor to notice is that Apple’s personal M-series chips that it has been utilizing in Macs since November 2020 are thought of safer than Intel processors. Nonetheless, malware, dubbed Silver Sparrow, was discovered on the M1 Mac quickly after launch so even Apple’s personal chips are usually not immune.
Curious to know what Mac viruses are on the market, maybe since you had been considering you may spy some suspicious processes or malware names in Exercise Monitor in your Mac? On this article we are going to endeavour to present you a whole checklist.
Mac malware in 2023
XMRig
When: February 2023. What: Crypto-mining software program connected to pirated copies of Ultimate Lower Professional which are downloaded from unauthorized distribution factors on the web. XMRig is definitely a authentic, open-source utility, however on this illegitimate use it’s working within the background mining, which impacts efficiency of the Mac. Mined cryptocurrency is shipped to the attacker’s pockets. The malware can keep away from detection by Exercise Monitor app by stopping working when Exercise Monitor launches and relaunching when the consumer quits Exercise Monitor. Apple says it has up to date macOS’s Xprotect to catch this malware. Who: Individuals who obtain pirated variations of Ultimate Lower Professional utilizing a torrent shopper. Extra right here: Pirated copies of Ultimate Lower Professional could infect your Mac.
Mac malware in 2022
Alchimist
When: October 2022. What: Gives a backdoor onto the goal system. Focusing on a vulnerability in a third occasion Unix device. Who: Very particular goal as pkexec isn’t discovered on Macs.
Lazarus
When: August 2022. What: Malware disguised as job postings. Who: Focusing on Coinbase customers and Crypto.com.
VPN Trojan
When: July 2022. What: VPN app with two malicious binaries: ‘softwareupdated’ and ‘covid’.
CloudMensis/BadRAT
When: July 2022. What: Spyware and adware downloader that makes use of public cloud storage providers reminiscent of Dropbox, Yandex Disk and pCloud. Exploited CVE-2020-9934 which was closed macOS Catalina 10.5.6 in August 2020.
CrateDepression
When: Might 2022. What: Provide chain assault with screencapture, keylogging, distant file retrieval. Who: Focused the Rust growth neighborhood.
Pymafka
When: Might 2022. What: Hoping that customers may mistype and obtain the malware as an alternative of authentic pykafka. Who: Focusing on PyPI registry.
oRAT
When: April 2022. What: Distributed through a Disk Picture masquerading as a group of Bitget Apps. Who: Focusing on playing web sites.
Gimmick
When: March 2022. What: Distributed as a CorelDraw file that was hosted on a Google Drive. Who: Focusing on protest teams in Asia.
DazzleSpy
When: January 2022. What: Included code for looking out and writing recordsdata, dumping the keychain, working a distant desktop and extra. Learn extra right here: Patched Mac malware sheds gentle on scary backdoor for hackers. Who: Focusing on supporters of democracy in Hong Kong.

ChromeLoader
When: January 2022. What: Chrome browser extension that might steal info, hijack the search engine queries, and serve adware.
Mac malware in 2021
macOS.Macma
When: November 2021. What: Keylogger, display capturer, display capturer and backdoor. Who: Targetting supporters of pro-democracy activism in Hong Kong.
OSX.Zuru
When: September 2021. What: Trojan that unfold disguised as iTerm2 app. Microsoft’s Distant Desktop for Mac was additionally trojanized with the identical malware. Who: Unfold through sponsored internet hyperlinks and hyperlinks within the Baidu search engine.
XCSSET Up to date
When: Might 2021 (initially from August 2020). What: Used a zero-day vulnerability in Safari. See: macOS 11.4 patches flaws exploited by XCSSET malware. Who: Geared toward Chinese language playing websites.
XLoader
When: July 2021. What: The XLoader malware was probably the most prevalent items of Home windows malware to have been confirmed to run on macOS. XLoader is a variant of Formbook, a program used to steal login credentials, report keystrokes, and obtain and execute recordsdata.
WildPressure
When: July 2021. What: New multi-platform model of Milum Trojan embedded in a Python file. Who: Focusing on Center East activists.
XcodeSpy
When: March 2021. What: A Trojan hidden in Xcode tasks in GitHub had the potential to unfold among the many Macs of iOS builders. As soon as put in a malicious script runs that installs an “EggShell backdoor”. As soon as open the Mac’s microphone, digital camera and keyboard will be hyjacked and recordsdata will be ship to the attacker. The malware was present in a ripped model of TabBarInteraction. Learn extra right here: New Mac malware targets iOS builders. Who: Assault on iOS builders utilizing Apple’s Xcode.
Silver Toucan/WizardUpdate/UpdateAgent
When: February 2021. What: Adload dropper that was notarized by Apple and used a Gatekeeper bypass.
Pirri/GoSearch22
When: February 2021. What: Based mostly on Pirri and generally known as GoSearch22 contaminated Macs would see undesirable adverts. Extra info right here: M1 Macs face first recorded malware.
Silver Sparrow
When: January 2021. What: Malware focusing on Macs outfitted with the M1 processor. Used the macOS Installer Javascript API to execute instructions. In accordance with Malwarebytes, by February 2021 Silver Sparrow had already contaminated 29,139 macOS programs in 153 nations, a lot of the contaminated Macs being within the US, UK, Canada, France and Germany. Extra particulars right here: What you want to find out about Silver Sparrow Mac malware.

Foundry
OSAMiner
When: January 2021 (however first detected in 2015). What: Cryptocurrency miner distributed through pirated copies of widespread apps together with League of Legends and Microsoft Workplace.
ElectroRAT
When: January 2021. What: Distant Entry Trojan focusing on a number of platforms together with macOS. Who: Focusing on cryptocurrency customers.
Mac malware in 2020
GravityRAT
When: October 2020. What: GravityRAT was an notorious Trojan on Home windows, which, amongst different issues, had been utilized in assaults on the navy. It arrived on Macs in 2020. The GravityRAT Trojan can add Workplace recordsdata, take automated screenshots and report keyboard logs. GravityRAT makes use of stolen developer certificates to bypass Gatekeeper and trick customers into putting in authentic software program. The Trojan is hidden in copies of varied authentic packages developed with .internet, Python and Electron. We now have extra details about GravityRAT on the Mac right here.
XCSSET
When: August 2020. What: Mac malware unfold by Xcode tasks posted on Github. The malware – a household of worms generally known as XCSSET – exploited vulnerabilities in Webkit and Knowledge Vault. Would search to entry info through the Safari browser, together with login particulars for Apple, Google, Paypal and Yandex providers. Different varieties of info collected consists of notes and messages despatched through Skype, Telegram, QQ and Wechat. Extra info right here.
ThiefQuest (aka EvilQuest)
When: June 2020. What: ThiefQuest, which we talk about right here: Mac ransomware ThiefQuest/EvilQuest may encrypt your Mac, was Ransomware spreading on the Mac through pirated software program discovered on a Russian torrent discussion board. It was initially regarded as Mac ransomware – the primary such case since 2017 – besides that it didn’t act like ransomware: it encrypted recordsdata however there was no technique to show you had paid a ransom and no technique to subsequently unencrypted recordsdata. It turned out that moderately than the aim of ThiefQuest being to extort a ransom, it was really making an attempt to acquire the information. Often known as ‘Wiper’ malware this was the primary of its sort on the Mac.
Mac malware in 2019
NetWire and Mokes
When: July 2019. What: These had been described by Intego as “backdoor malware” with capabilites reminiscent of keystoke logging and screenshot taking. They had been a pair of Firefox zero-days that focused these utilizing cryptocurrancies. Additionally they bypassed Gatekeeper. backdoor” malware
LoudMiner (aka Hen Miner)
When: June 2019. What: This was a cryptocurrency miner that was distributed through a cracked installer for Ableton Dwell. The cryptocurrency mining software program would try to make use of your Mac’s processing energy to earn a living.
OSX/NewTab
When: June 2019. What: This malware tried so as to add tabs to Safari. It was additionally digitally signed with a registered Apple Developer ID.
OSX/Linker
When: Might 2019. What: It exploited a zero-day vulnerability in Gatekeeper to put in malware. The “MacOS X GateKeeper Bypass” vulnerability had been reported to Apple that February, and was disclosed by the one that found it on 24 Might 2019 as a result of Apple had failed to repair the vulnerability inside 90 days. Who: OSX/Linker tried to take advantage of this vulnerability, but it surely was by no means actually “within the wild”.
CookieMiner
When: January 2019. What: The CookieMiner malware may steal a customers password and login info for his or her cyberwallets from Chrome, get hold of browser authentication cookies related to cryptocurrency exchanges, and even entry iTunes backups containing textual content messages to be able to piece collectively the knowledge required to bypass two-factor authentication and achieve entry to the sufferer’s cryptocurrency pockets and steal their cryptocurrency. Unit 42, the safety researchers who recognized it, counsel that Mac customers ought to clear their browser caches after logging in to monetary accounts. Because it’s related to Chrome we additionally suggest that Mac customers select a special browser. Discover out extra about CookieMiner Mac malware right here.
Mac malware in 2018
SearchAwesome
When: 2018. What: OSX.SearchAwesome was a type of adware that targets macOS programs and will intercept encrypted internet visitors to inject adverts.
Mac Auto Fixer
When: August 2018. What: Mac Auto Fixer was a PiP (Probably Undesirable Program), which piggybacks on to your system through bundles of different software program. Discover out extra about it, and how you can eliminate it, in What’s Mac Auto Fixer?
OSX/CrescentCore
When: June 2018. What: This Mac malware was discovered on a number of web sites, together with a comic-book-download web site in June 2019. It even confirmed up in Google search outcomes. CrescentCore was disguised as a DMG file of the Adobe Flash Participant installer. Earlier than working it might verify to see if it inside a digital machine and would seems to be for antivirus instruments. If the machine was unprotected it might set up both a file known as LaunchAgent, an app known as Superior Mac Cleaner, or a Safari extension. CrescentCore was capable of bypass Apple’s Gatekeeper as a result of it had a signed developer certificates assigned by Apple. That signature was finally revoked by Apple. But it surely reveals that though Gatekeeper ought to cease malware getting by, it may be finished. Once more, we notice that Adobe ended assist for Adobe Flash on 31 December 2020, so this could imply fewer circumstances of malware being disguised because the Flash Participant.
Mshelper
When: Might 2018. What: Cryptominer app. Contaminated customers seen their followers spinning notably quick and their Macs working hotter than common, a sign {that a} background course of was hogging sources.
OSX/Shlayer
When: February 2018. What: Mac adware that contaminated Macs through a faux Adobe Flash Participant installer. Intego identifed it as a brand new variant of the OSX/Shlayer Malware, whereas it might even be refered to as Crossrider. In the midst of set up, a faux Flash Participant installer dumps a replica of Superior Mac Cleaner which tells you in Siri’s voice that it has discovered issues together with your system. Even after eradicating Superior Mac Cleaner and eradicating the varied elements of Crossrider, Safari’s homepage setting continues to be locked to a Crossrider-related area, and can’t be modified. Since 31 December 2020 Flash Participant has been discontinued by Adobe and it not supported, so you may make sure that for those who see something telling you to put in Flash Participant please ignore it. You possibly can learn extra about this incident right here.
MaMi
When: January 2018. What: MaMi malware routes all of the visitors by malicious servers and intercepts delicate info. This system installs a brand new root certificates to intercept encrypted communications. It may possibly additionally take screenshots, generate mouse occasions, execute instructions, and obtain and add recordsdata.
Meltdown & Spectre

Foundry
When: January 2018. What: Apple confirmed it was one among quite a few tech corporations affected, highlighting that: “These points apply to all fashionable processors and have an effect on practically all computing units and working programs.” The Meltdown and Spectre bugs may permit hackers to steal information. Meltdown would contain a “rogue information cache load” and might allow a consumer course of to learn kernel reminiscence, based on Apple’s temporary on the topic. Spectre might be both a “bounds verify bypass,” or “department goal injection” based on Apple. It may doubtlessly make gadgets in kernel reminiscence accessible to consumer processes. They are often doubtlessly exploited in JavaScript working in an internet browser, based on Apple. Apple issued patches to mitigate the Meltdown flaw, regardless of saying that there isn’t any proof that both vulnerability had been exploited. Extra right here: Meltdown and Spectre CPU flaws: Methods to shield your Mac and iOS units.
Mac malware in 2017
Dok
When: April 2017. What: macOS Malicious program appeared to have the ability to bypass Apple’s protections and will hijack all visitors getting into and leaving a Mac with out a consumer’s information – even visitors on SSL-TLS encrypted connections. OSX/Dok was even signed with a sound developer certificates (authenticated by Apple) based on CheckPoint’s weblog publish. It’s seemingly that the hackers accessed a authentic builders’ account and used that certificates. As a result of the malware had a certificates, macOS’s Gatekeeper would have acknowledged the app as authentic, and due to this fact not prevented its execution. Apple revoked that developer certificates and up to date XProtect. OSX/Dok was focusing on OS X customers through an electronic mail phishing marketing campaign. One of the simplest ways to keep away from falling foul to such an makes an attempt is just not to reply to emails that require you to enter a password or set up something. Extra right here.
X-agent
When: February 2017. What: X-agent malware was able to stealing passwords, taking screenshots and grabbing iPhone backups saved in your Mac. Who: The malware apparently focused members of the Ukrainian navy and was thought to be the work of the APT28 cybercrime group, based on Bitdefender.
MacDownloader
When: February 2017. What: MacDownloader software program present in a faux replace to Adobe Flash. When the installer was run customers would get an alert claiming that adware was detected. When requested to click on to “take away” the adware the MacDownloader malware would try to transmit information together with the customers Keychain (usernames, passwords, PINs, bank card numbers) to a distant server. Who: The MacDownloader malware is assumed to have been created by Iranian hackers and was particularly targetted on the US defence trade. It was situated on a faux web site designed to focus on the US defence trade.
Phrase macro virus
When: February 2017. What: PC customers have needed to cope with macro viruses for a very long time. Functions, reminiscent of Microsoft Workplace, Excel, and Powerpoint permit macro packages to be embedded in paperwork. When these paperwork are opened the macros are run mechanically which might trigger issues. Mac variations of those packages haven’t had a problem with malware hid in macros as a result of since when Apple launched Workplace for Mac 2008 it eliminated macro assist. Nonetheless, the 2011 model of Workplace reintroduced macros, and in February 2017 there was malware found in a Phrase macro inside a Phrase doc about Trump. If the file is opened with macros enabled (which doesn’t occur by default), it would try to run python code that might have theoretically carry out capabilities reminiscent of keyloggers and taking screenshots. It may even entry a webcam. The prospect of you being contaminated on this manner could be very small, except you have got acquired and opened the file referred to (which might shock us), however the level is that Mac customers have been focused on this manner.
Fruitfly
When: January 2017. What: Fruitfly malware may seize screenshots and webcam photographs, in addition to in search of details about the units related to the identical community – after which connects to them. Malwarebytes claimed the malware may have been circulating since OS X Yosemite was launched in 2014.
Mac malware in 2016
Pirrit
When: April 2016. What: OSX/Pirrit was apparently hidden in cracked variations of Microsoft Workplace or Adobe Photoshop discovered on-line. It might achieve root privileges and create a brand new account to be able to set up extra software program, based on Cybereason researcher Amit Serper on this report.
Safari-get
When: November 2016. What: Mac-targeted denial-of-service assaults originating from a faux tech assist web site. There have been two variations of the assault relying in your model of macOS. Both Mail was hijacked and compelled to create huge numbers of draft emails, or iTunes was compelled to open a number of occasions. Both manner, the top objective is to overload system reminiscence and pressure a shutdown or system freeze.

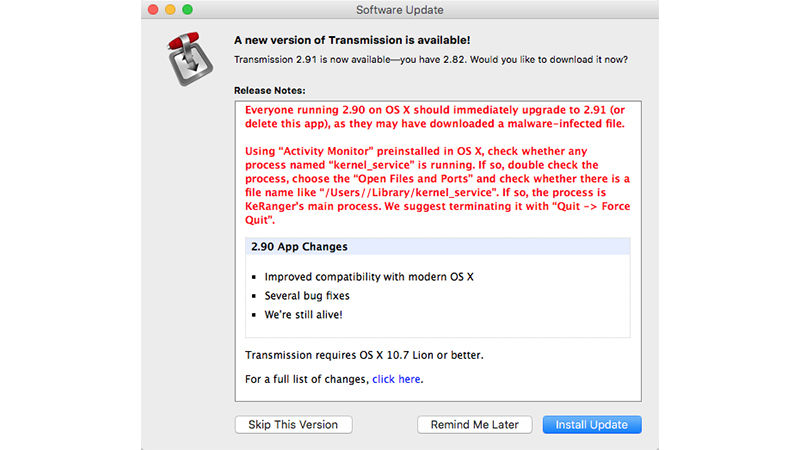
KeRanger
When: March 2016. What: KeRanger was ransomware (now extinct). For a very long time ransomware was an issue that Mac homeowners didn’t have to fret about, however the first ever piece of Mac ransomware, KeRanger, was distributed together with a model of a chunk of authentic software program: the Transmission torrent shopper. Transmission was up to date to take away the malware, and Apple revoked the GateKeeper signature and up to date its XProtect system, however not earlier than quite a few unfortunate customers obtained stung. We talk about how you can take away Ransomware right here.
Older Mac malware
SSL, Gotofail error
When: February 2014. What: The issue stemmed from Apple’s implementation of a primary encryption characteristic that shields information from snooping. Apple’s validation of SSL encryption had a coding error that bypassed a key validation step within the internet protocol for safe communications. There was an additional Goto command that hadn’t been closed correctly within the code that validated SSL certificates, and consequently, communications despatched over unsecured Wi-Fi hotspots might be intercepted and skim whereas unencrypted. Apple shortly issued an replace to iOS 7, however took longer to issued an replace for Mac OS X, regardless of Apple confirming that the identical SSL/TSL safety flaw was additionally current in OS X. Who: To ensure that the sort of assault to be attainable, the attacker must be on the identical public community. Learn extra concerning the iPad and iPhone safety flaw right here.
OSX/Tsnunami.A
When: October 2011. What: OSX/Tsnunami.A was a brand new variant of Linux/Tsunami, a malicious piece of software program that commandeers your laptop and makes use of its community connection to assault different web sites. Extra info right here.
OSX.Revir.A
When: September 2011. What: Posing as a Chinese language-language PDF, the nasty piece of software program installs backdoor entry to the pc when a consumer opens the doc. Extra right here.
Flashback trojan
When: September 2011. What: Flashback is assumed to have been created by the identical folks behind the MacDefender assault and will use an unpatched Java vulnerability to put in itself. Learn extra right here: What you want to know concerning the Flashback trojan. Who: Apparently greater than 500,000 Macs had been contaminated by April 2012.
MacDefender
When: Might 2011. What: Trojan Horse phishing rip-off that presupposed to be a virus-scanning software. Was unfold through search engine marketing (search engine optimization) poisoning.
BlackHole RAT
When: February 2011. What: Extra of a proof-of-concept, however a prison may discover a technique to get a Mac consumer to put in it and achieve distant management of the hacked machine. BlackHole was a variant of a Home windows Trojan known as darkComet. Extra info right here: Hacker writes easy-to-use Mac Trojan.
For extra details about how Apple protects your Mac from safety vulnerabilities and malware learn:
Do Macs want antivirus software program.

